Six Russian GRU Agents Indicted in Connection With NotPetya Attack
The U.S. Department of Justice has charged six members of the Russian Main Intelligence Directorate (GRU) in connection with the June 2017 "NotPetya" cyberattack. The notorious malware release led to prolonged shutdowns across the APM Terminals and Maersk Line business IT networks, among many other serious impacts worldwide.
On June 27, 2017, the destructive NotPetya malware attack hit critical infrastructure and government targets in Ukraine. It then spread uncontrolled between corporate computer networks, affecting dozens of unrelated companies worldwide. Among other organizations, it impacted operations at Maersk, APMT, Fedex subsidiary TNT Express, and U.S. pharmaceutical company Merck. The U.S.-based impacts on shoreside business came to nearly $1 billion, and the shutdown cost Maersk Group an estimated $300 million across its global maritime operations.
The Kremlin has previously denied any involvement in the attack, dismissing criticism as a "Russophobic campaign."
“No country has weaponized its cyber capabilities as maliciously or irresponsibly as Russia, wantonly causing unprecedented damage to pursue small tactical advantages and to satisfy fits of spite,” said Assistant Attorney General for National Security John C. Demers. “Today the department has charged these Russian officers with conducting the most disruptive and destructive series of computer attacks ever attributed to a single group, including by unleashing the NotPetya malware. No nation will recapture greatness while behaving in this way.”
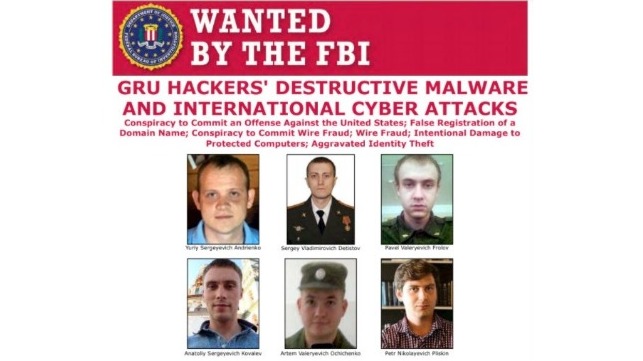
The GRU officers who allegedly developed NotPetya were named as Petr Nikolayevich Pliskin, Pavel Valeryevich Frolov, Sergey Vladimirovich Detistov and Yuriy Sergeyevich Andrienko. Two more individuals - Anatoliy Sergeyevich Kovalev and Artem Valeryevich Ochichenko - were charged in connection with unrelated hacking campaigns.
In addition to their activities related to NotPetya, the six officers were allegedly involved in hacking other foreign targets. These attacks included destructive malware attacks targeting Ukrainian utility companies and government agencies in 2015-16; spearphishing and hack-and-leak operations targeting French politicians and government entities in the run-up to the 2017 French elections; spearphishing and malicious app attacks against officials and participants in the PyeongChang 2018 Winter Olympics; and a spearphishing campaign aimed at the investigation into Russian use of nerve agents on British soil in 2018.

that matters most
Get the latest maritime news delivered to your inbox daily.
If arrested in the United States or extradited, each would face seven charges - conspiracy to conduct computer fraud and abuse, conspiracy to commit wire fraud, wire fraud, damaging protected computers and aggravated identity theft. The maximum penalty for wire fraud is 20 years in jail.
The same GRU division - Unit 74455 ("Sandworm" or "Fancy Bear") - allegedly contributed to the successful phishing attack on the Democratic National Committee and other electoral interference campaigns during the 2016 U.S. presidential election, according to cybersecurity consultancy CrowdStrike. In 2018, Special Counsel Robert Mueller indicted 12 officers from Units 74455 and 26165 in connection with that campaign, including Anatoliy Sergeyevich Kovalev. Though the new charges released Monday include allegations of interference in elections overseas, they do not reference this earlier activity.
